Keyword Exploration Portal Asikrofil Analyzing Digital Identity Searches

Asikrofil presents a structured approach to analyzing digital identity searches. The framework highlights reproducibility, data normalization, and privacy-aware metrics. It isolates genuine signals from noise through a data-driven workflow that emphasizes governance and chain-of-custody. The method balances granularity with cross-session comparability, enabling incident response and threat hunting. Yet questions linger about bias, scalability, and real-world applicability, inviting further scrutiny into how these analyses withstand evolving privacy and ethical constraints.
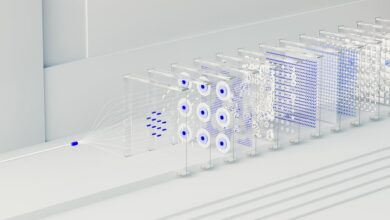
How Asikrofil Analyzes Digital Identity Searches
Asikrofil analyzes digital identity searches through a structured, data-driven workflow that isolates search activity signals from noise. The methodology emphasizes reproducibility and transparency, coupling asikrofil workflows with rigorous validation. Data are normalized to enable cross-session comparisons, enabling stable keyword normalization across environments. Findings are presented objectively, supporting informed decisions while preserving user autonomy and freedom within a principled analytical framework.
Key Metrics Driving Identity-Related Insights
Key metrics underpinning identity-related insights are selected to balance granularity with comparability, ensuring that signals reflect genuine user behavior rather than incidental activity. The approach emphasizes systematic measurement, cross‑validation, and transparent definitions. It highlights privacy risks and data minimization as guardrails, ensuring analyses remain responsible. Ultimately, metric selection supports disciplined interpretation, enabling informed decisions while preserving user autonomy and analytical integrity.
Practical Use Cases for Forensic Keyword Insights
Practical use cases for forensic keyword insights span incident response, threat hunting, and post-incident analysis, where structured keyword patterns illuminate attacker methodologies, timing, and targets.
The approach supports documenting data privacy considerations and data governance implications, guiding evidence collection, chain-of-custody, and risk assessment.
Findings enable disciplined remediation, cross-functional decision-making, and policy refinement while sustaining principled, transparent investigative practices.
Evaluating Privacy and Ethical Considerations in Asikrofil
In evaluating privacy and ethical considerations in Asikrofil, a rigorous framework is required to balance investigative utility with individual rights and data governance.
The analysis examines privacy boundaries and consent norms, identifying where data collection remains legitimate, proportionate, and transparent.
Methodical assessment highlights governance gaps, risk mitigation, and accountability mechanisms to sustain public trust while enabling investigative insights within legal and ethical limits.
Conclusion
Asikrofil’s methodical framework distills raw search signals into reproducible, privacy-conscious indicators of identity-related activity. By normalizing data, enforcing governance, and tracing lineage through robust chain-of-custody, it provides transparent insights while minimizing noise. The investigative cadence—data collection, validation, and contextual interpretation—permits precise threat hunts and post-incident analyses. In this measured landscape, clarity acts as a beacon, a lighthouse of verifiable metrics guiding stakeholders through the fog of digital searches.