Online Identity Insight Guide annalizababy10 Exploring Digital Profile Searches

Online Identity Insight Guide annalizababy10 frames digital footprints as a structured, enduring profile. The piece introduces a Find-Assess-Rank approach to catalog sources, evaluate relevance, and expose privacy gaps with disciplined rigor. It advocates practical privacy hygiene and proactive control, aiming to transform scattered data into a credible online identity anchored in verifiable presence. The methodical path invites careful consideration of trade-offs and what remains hidden as one moves forward.
What Your Digital Footprint Really Looks Like
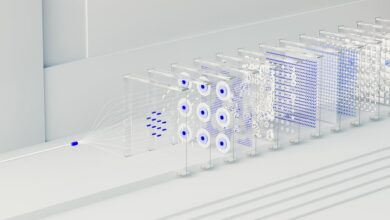
A digital footprint is the trace left by online actions, aggregating data points from searches, posts, comments, and profile activity to form a persistent profile.
The representation is structured yet opaque, highlighting patterns across platforms.
Privacy visibility fluctuates as settings change, while data exposure shifts with new accounts, breaches, and third-party analytics.
This portrait emphasizes accountability, measurement, and the need for proactive digital hygiene.
Audit Steps: Find, Assess, and Rank Your Online Presence
Audit steps for online presence require a systematic approach to uncover, evaluate, and prioritize digital traces. The process enumerates sources, inventories content, and assigns relevance scores, enabling objective comparison. Assessments expose gaps in privacy governance and opportunities for risk mitigation. Ranking clarifies priorities, guiding strategic reputation management while preserving freedom of expression and measured control over informational footprints. Analytical rigor yields actionable, defensible conclusions.
Cleaning and Controlling: Privacy Practices That Work
Building on the audit framework for online presence, this section translates findings into concrete privacy habits and controls. The analysis emphasizes privacy hygiene and data hygiene as core disciplines, detailing consistent practices: minimize data exposure, enforce configurable privacy settings, conduct regular footprint reviews, and document control changes. Systematic habits reduce risk, support autonomy, and enable sustainable, freedom-centered digital self-management.
From Search to Opportunity: Presenting a Trusted Online Identity
This section analyzes how a searchable footprint can be transformed into a credible digital profile by aligning data points with clearly defined trust criteria, verifying sources, and curating results to emphasize reliability over novelty.
The discussion models identity verification as a procedural standard, linking consistent signals to a coherent narrative, while reputation management scaffolds credibility, ensuring opportunities arise from verifiable, transparent online presence rather than speculation.
Conclusion
In a quiet lab of data points, coincidence emerges: a buried comment matches a dated credential, a post echoes a trusted source, and a cautious user revises a profile just as a recruiter searches for them. The process—Find, Assess, Rank, then Clean—turns scattered echoes into a coherent signal. When privacy hygiene guides each action, the accidental overlaps become deliberate alignments, yielding a verifiable online identity that withstands scrutiny and opens measured opportunities.