Social Media ID Exploration Node bdr767243202 Unlocking Profile Trace Data

The discussion centers on Social Media ID Exploration Node bdr767243202 and its approach to unlocking profile trace data. It outlines how identifiers map to actions across sessions and devices, with emphasis on traceability and repeatability. Methods are described in a data-driven, concise manner, highlighting data points, limits, and ethical guardrails. The goal is to assess patterns responsibly, yet the implications and boundaries remain open to further scrutiny and refinement. This tension invites continued examination.
What Is Profile Trace Data and the Node bdr767243202
Profile trace data refers to the records that capture how users interact with a social media platform, including actions such as views, clicks, and timing patterns.
This entry notes Node exploration as a structured process to examine interaction signals, sequences, and dependencies.
Data-driven observations guide interpretation, ensuring concise insights.
The objective is clarity, enabling freedom-minded readers to understand patterns without extraneous speculation.
How ID Tracing Works: Techniques, Data Points, and Limits
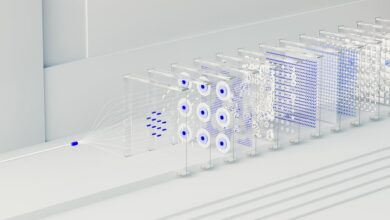
How ID tracing operates on social platforms hinges on aggregating and correlating signals across sessions to map user identifiers to actions. Techniques include deterministic matching, probabilistic inference, and event stitching, while data points encompass timestamps, device fingerprints, and interaction cues. Limits arise from privacy controls, data sparsity, and model bias. conceptual mapping and data provenance anchor interpretation, ensuring traceability and accountability.
Use Cases for Researchers: Mapping Digital Footprints and Behavioral Insights
Researchers can leverage mapped digital footprints to quantify patterns across platforms, sessions, and devices, enabling systematic analysis of user behavior while maintaining traceability to underlying signals identified in prior ID-tracing work.
This use case emphasizes data collection strategies, bias mitigation, privacy awareness, and consent considerations, supporting reproducible findings and cross-platform comparisons across researchers pursuing objective, freedom-friendly insights.
Privacy, Ethics, and Responsible Data Handling in ID Exploration
Privacy, ethics, and responsible data handling in ID exploration require a principled, evidence-based framework. The analysis emphasizes privacy concerns, consent mechanisms, and de identification protocols as core controls. Ethics considerations guide risk assessment, data minimization, and transparent methodologies. A detached approach ensures reproducibility, while safeguarding participant welfare. Methodical evaluation informs policy recommendations, balancing research value with individual rights and proportional safeguards.
Conclusion
In the final ledger, profile trace data reveals a disciplined pattern: signals accumulate, devices align, actions converge. The node bdr767243202 maps those threads with methodical care, exposing how identifiers trace behavior without revealing the entire silhouette. Yet gaps persist—latent links, evolving privacy safeguards, and shifting platforms invite caution. Researchers sense the impending edge of insight and the risk of overreach. The data invites further study, with strict ethics guiding every measured step toward responsible clarity.