Account Analysis Node c00hha0220120134 Exploring Digital Identity
The Account Analysis Node c00hha0220120134 explores how identities are recognized across systems, linking credentials to actions and mapping data attributes to trust levels. It examines verification, authentication, authorization, and consent as core pillars. Technologies and standards that enable governance are assessed for interoperability, security, and privacy by design. The framework balances usability with risk controls, highlighting context-aware verification within secure ecosystems, and invites consideration of practical implications that warrant further scrutiny.
What Is Digital Identity in Practice
What is digital identity in practice? The construct describes how individuals are recognized across systems, linking credentials to actions. Data-driven models map attributes to trust levels, enabling efficient governance. Identity verification confirms claimed traits, while access privileges determine permitted operations. This framework supports secure interactions, minimizes risk, and enhances user autonomy by aligning verification rigor with contextual requirements and evolving security policies.
Assessing the Trust Pillars: Authentication, Authorization, and Consent
Assessing the Trust Pillars: Authentication, Authorization, and Consent entails a structured evaluation of how each mechanism supports secure, user-centered access within digital ecosystems. The analysis highlights authentication challenges, quantifying success rates, failure modes, and friction metrics. It also examines consent granularity, governance controls, and trade-offs between usability and privacy, guiding defenders toward principled, freedom-oriented, data-driven access decisions.
Technologies and Standards Shaping Identity Governance
Technologies and standards shaping identity governance encompass a suite of interoperable frameworks, protocols, and policy models that enable scalable, secure, and auditable access across organizations. This landscape emphasizes open standards, interoperable APIs, and governance modals that constrain or empower automation.
Tokenization systems improve data minimization, while privacy by design embeds protective controls throughout lifecycle workflows, aligning efficiency with risk-aware, freedom-respecting compliance.
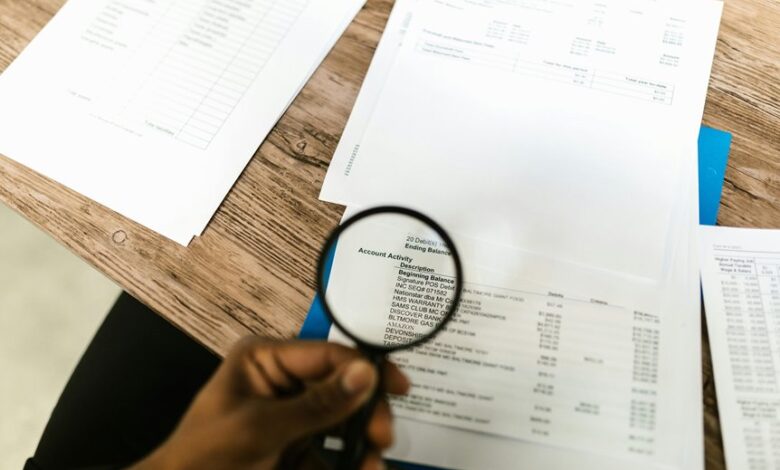
Navigating Risks, Privacy, and User Experience at Scale
As organizations expand identity-enabled workflows, balancing risk, privacy, and user experience becomes a defining constraint on scale. The analysis emphasizes privacy ergonomics as a design lens, aligning controls with user expectations while preserving security posture. Risk visualization dashboards translate complex threat signals into actionable metrics, enabling governance teams to prioritize mitigations without compromising performance or freedom.
Conclusion
Digital identity governance increasingly binds credentials to actions across ecosystems, balancing security with usability. A notable statistic: organizations that implement context-aware verification reduce fraudulent access by up to 40% while maintaining user satisfaction. The synthesis shows trust pillars—authentication, authorization, and consent—are interdependent, not siloed. Standards-driven interoperability enables scalable governance and privacy-by-design, even as threats evolve. Contextual controls, data-driven models, and adaptive governance will determine resilience in secure, user-centric digital environments.