Fraud Research Node Check Scammer Phone Number Exploring Verified Patterns

Fraud Research Node applies a disciplined approach to check scammer phone numbers by verifying validity, timing, and source metadata. Signals are collected, filtered, and cross-validated against known patterns to produce robust cohorts. The process emphasizes traceability and reproducibility, with privacy safeguards guiding data handling. Findings support risk assessment and policy refinement for stakeholders, while unanswered questions about evolving techniques compel further scrutiny. The implications hinge on stable methodology amid shifting fraud tactics.
Fraud Research Node’s Approach to Phone-Number Verification
Fraud Research Node uses a structured verification protocol to assess phone numbers, prioritizing accuracy and traceability over speed. The approach emphasizes reproducible steps, cross-referencing sources, and documented criteria to determine the validity of a phone number. When data inconsistencies arise, the framework analyzes potential verification failure causes and records outcomes for transparency and ongoing improvement.
Tracing Origins, Timing, and Metadata in Fraud Signals
Tracing origins, timing, and metadata in fraud signals requires a disciplined, evidence-based assessment of how signals are generated, logged, and interpreted. Incoming signals undergo careful timing analysis and source tracing to support pattern verification. Privacy safeguards and ethics govern data handling, while practical uses for stakeholders emphasize transparency, reproducibility, and accountability in signal interpretation and risk decisions.
Turning Raw Signals Into Verified Patterns and Consumer Insights
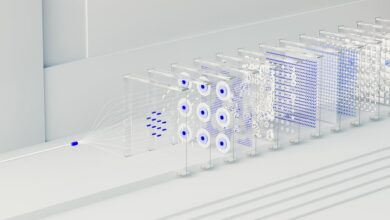
What constitutes a reliable transformation from raw signals to actionable patterns and consumer insights? The process hinges on systematic collection, rigorous filtering, and reproducible methods. Analysts identify patterns through cross-domain signals and contextual validation. They compare signals across cohorts, test hypotheses, and assess stability. Validating signals ensures robustness, enabling precise, decision-relevant consumer insights for fraud resilience and policy refinement.
Privacy Safeguards, Ethics, and Practical Uses for Stakeholders
Effective privacy safeguards, ethics, and practical uses for stakeholders require a structured alignment of data governance, compliance, and risk assessment to ensure that fraud research methods protect individuals while enabling reliable insights.
The analysis emphasizes privacy safeguards, ethics considerations, tracing origins, and metadata handling, balancing transparency with protection, enabling responsible collaboration among researchers, regulators, and organizations in pursuit of accurate, lawful, and privacy-respecting fraud insights.
Conclusion
The Fraud Research Node adopts a disciplined, evidence-based workflow to validate scammer phone numbers through cross-checked validity, timing, and metadata, producing robust patterns rather than isolated signals. By triangulating sources and documenting traceable criteria, the approach strengthens reproducibility and policy relevance. Privacy safeguards and ethics remain integral, ensuring responsible use by regulators and organizations. The resulting consumer insights, while precise, are powerful enough to deter fraud at scale—an exponential improvement over prior, fragmented detection methods.