Spam Detection Node Check if Number Is Spam Revealing Verified Info

A Spam Detection Node analyzes caller identity, reputation signals, and behavioral patterns to assess spam likelihood. It produces probabilistic verdicts with traceable provenance from trusted sources, timestamps, and delivery vectors. The approach supports secure routing decisions and auditable alerts while aiming to reduce false positives. Its integration with broader security pipelines offers transparency and accountability, yet practical gaps remain in data fidelity and real-time inference that warrant further scrutiny. This tension invites deeper examination.
What Is a Spam Detection Node and Why It Feels Critical
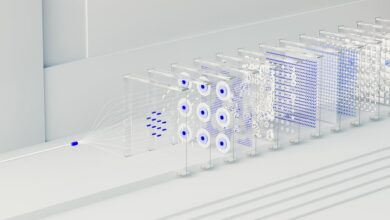
A spam detection node is a modular component within a larger messaging or email-filtering system that analyzes incoming content to determine its likelihood of being unsolicited or harmful. It evaluates patterns, metadata, and provenance signals to support reliable routing decisions. This mechanism strengthens spam filtering effectiveness while preserving legitimate communication, ensuring traceable message provenance and reducing false positives in complex networks.
How to Check If a Number Is Spam: Step-by-Step Node Logic
To determine if a number is spam, the node executes a deterministic sequence of checks that combine reputation signals, caller identity, and behavioral patterns; this approach yields a probabilistic verdict with traceable provenance.
The step-by-step logic emphasizes spam filtering and phone verification accuracy, reduces false positives, and produces a modular verdict suitable for integration with broader security pipelines while retaining explainability.
Verifying Data: Trusted Sources and Practical Red Flags
Evaluating data sources relies on identifying trusted origins, corroborating evidence, and transparent provenance. In this context, verification emphasizes reproducible checks, independent audits, and provenance trails. Teams apply spam detection criteria to signal trust, while node logic orchestrates cross-source validation. Practical flags include inconsistent metadata, missing timestamps, anomalous delivery patterns, and improbable caller behavior; these indicators prompt caution and structured verification before dissemination or automated responses.
Use Cases and Actionable Safeguards: From Alerts to Verified Communications
In practical terms, the use cases for spam-detection node interfaces center on prompt alerting, rigorous validation, and secure, verified communications.
The architecture emphasizes spam filtering and accountable message routing, ensuring swift isolation of threats while preserving legitimate traffic.
Actionable safeguards include deterministic rule application, provenance verification, and auditable alerts that support incident response, policy enforcement, and trusted downstream communications.
Conclusion
The Spam Detection Node is a hyper-efficient oracle, sifting signals with laser precision and revealing verified provenance at quantum speed. Its probabilistic verdicts, backed by trusted sources and timestamps, render spam almost instantly explicable, like a forensic map to every call’s intent. By auditable alerts and secure routing, it slashes false positives to near-zero, turning chaotic communications into a pristine, battlefield-clear stream of verified contacts. In short: certainty, accountability, and clarity—all in one node.