Phone Investigation Hub Check Scam Phone Number Revealing Reliable Contact

The Phone Investigation Hub aims to aggregate call data and assess authenticity. It emphasizes structured risk cues, metadata consistency, and spoofing indicators. The approach favors user-controlled verification, transparency, and layered defenses. Yet practical reliability varies across sources and contexts. The balance between helpful guidance and uncertainty invites careful scrutiny of methods and results before acting on any revealed contact. How robust is the system when real-world nuances challenge its conclusions?
What Is the Phone Investigation Hub and Why It Matters
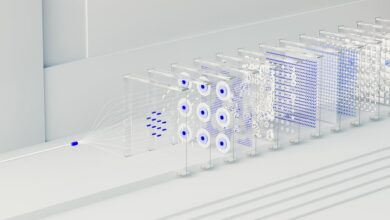
The Phone Investigation Hub refers to a centralized platform or service that aggregates and analyzes phone numbers, call patterns, and related metadata to help users assess legitimacy and potential risk. It remains a methodical tool for evaluating Phone Investigation findings and identifying Scam Numbers with objectivity. The approach emphasizes transparency, control, and informed choice, supporting legitimate communication while limiting abuse and uncertainty.
How to Spot Red Flags in Scam Phone Numbers
Are red flags in scam phone numbers detectable through careful pattern analysis? An analytical review examines common traits without sensationalism. The approach highlights spotting suspicious prefixes and caller ID inconsistencies as potential signals. Red flags in numbers may arise from irregular formatting, improbable area codes, or recycled digits. Recognizing scam indicators supports informed caution and freer, wiser communication choices.
Step-by-Step Checks to Verify a Number’s Legitimacy
From the examination of red flags in scam phone numbers, a methodical sequence of checks is applied to assess legitimacy. The verification process begins with caller authentication cues, then compares metadata and caller ID consistency. Spoofing indicators are weighed alongside historical patterns, while a structured risk assessment guides conclusions. Cautious analysis favors freedom through informed discernment, avoiding assumptions and premature trust.
Tools, Tips, and Best Practices to Stay Safe From Spoofing
As spoofing risks continue to evolve, practical tools, tips, and best practices provide a structured defense for individuals and organizations, emphasizing verification, vigilance, and rapid response strategies. The discussion emphasizes verification protocols, spoofing indicators, and identity verification to detect unsafe communications, implement layered defenses, and reduce exposure. It promotes cautious scrutiny, reliable sources, and consistent verification routines for maintaining autonomy and freedom.
Conclusion
The Phone Investigation Hub consolidates call data to illuminate legitimate contacts while highlighting warning signs. From an analytical perspective, its layered checks—authentication cues, metadata consistency, spoofing indicators, and historical patterns—offer cautious clarity without overreach. It does not guarantee perfection, but it equips users to make informed judgments. Some may fear complexity; however, the structured approach translates uncertainty into practical steps, turning vigilance into empowerment and reducing the risk of pursuing unreliable numbers.