Phone Monitoring Portal Check This Phone Number Unlocking Safe Contact Info

A Phone Monitoring Portal centralizes data such as calls, messages, location, and app activity, with an emphasis on consent, transparency, and user rights. Safely and legally checking a phone number requires purpose limitation, data minimization, and verified sources. Unlocking safe contact info should follow explicit consent, documented justification, and auditable procedures, all protected by access controls. The balance between utility and privacy remains delicate, inviting scrutiny of processes and safeguards as risk factors persist.
What a Phone Monitoring Portal Is and Isn’t
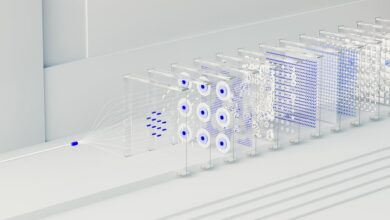
A phone monitoring portal is a software interface that centralizes access to device data, typically aggregating call logs, messages, location history, and app activity. It is a tool with limitations, clarifying roles, capabilities, and protections. Monitoring ethics and consent aware practices guide deployment, ensuring transparency, accountability, and user rights while avoiding intrusive overreach or misuse.
How to Check a Phone Number Safely and Legally
To determine a phone number’s validity and origin, one must follow a structured, legally compliant approach that emphasizes consent, purpose, and data protection. The analysis remains detached, focusing on check legality, privacy risks, and proportional data access. Emphasis rests on consent requirements, verifiable sources, and transparent purpose, ensuring lawful use while safeguarding individuals’ rights and minimizing unnecessary data exposure.
Unlocking Safe Contact Info: Step-by-Step and Best Practices
Unlocking Safe Contact Info requires a disciplined, methodical approach that prioritizes consent, purpose limitation, and data minimization. The analysis outlines steps and best practices for verifying sources, documenting purposes, and limiting exposure. It emphasizes secure handling, audit trails, and user rights. By adhering to these measures, unlocking safe contact info becomes a controlled process that respects autonomy while enabling responsible outreach.
Staying Privacy-Respectful and on the Right Side of Law
Staying privacy-respectful and on the right side of the law requires a disciplined approach to data handling, governance, and accountability that minimizes risk while preserving legitimate access.
The analysis emphasizes privacy preserving practices, consent first, and data minimization to ensure lawful compliance.
It favors transparent policies, auditable controls, and proportional data use, balancing freedom with rigorous regulatory alignment.
Conclusion
In the ledger of connections, the phone is a locked vault and the portal a careful custodian. Keys must be earned, not seized; transparency is the seal on every turn of the dial. Data flows resemble guarded rivers—brief, purposeful, and traceable. Consent is the compass, audit trails the map, access controls the gate. When used with restraint, the machinery serves safety; when misused, it becomes a shadowed alley, eroding trust and inviting all the echoes of risk.