Phone Verification Hub Check Spam Phone Number Revealing Trusted Data
A Phone Verification Hub aggregates numbers, metadata, and reputation signals to assess unwanted activity. It aims for impartial evaluation rather than hype. Signals include caller reputation, empirical spam scores, and corroborating data. The system emphasizes user autonomy and privacy safeguards. Yet questions remain about data sources, accuracy, and potential biases. If these tools can be trusted to guide decisions without coercion, what checks ensure reliable outcomes?
What Is Phone Verification Hub for Spam Checks
A phone verification hub for spam checks is a centralized system that aggregates phone numbers, metadata, and reputation signals to assess whether a number is associated with unwanted or deceptive activity. It operates with impartial data, emphasizing transparency over hype. scrupulous evaluation centers on spam checks and caller reputation, enabling informed decisions while preserving user autonomy and resisting coercive telemarketing narratives.
How to Spot a Spam Number Before Answering
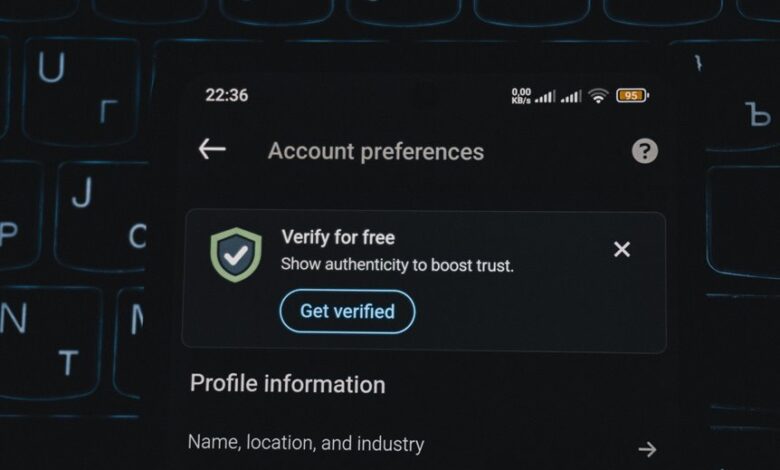
To spot a spam number before answering, one should check for common red flags and corroborating signals rather than rely on a single cue. The approach remains skeptical and data-driven, avoiding certainty from a lone call. Consider inconsistent caller information, odd timing, and unusual requests. Spam indicators and caller reputation emerge through pattern recognition, not isolated anecdotes, preserving user autonomy and control.
Revealing Trusted Data: From Caller ID to Reputation Scores
Revealing trusted data involves weighing multiple signals beyond a single identifier. In this context, data streams like caller reputation and empirical spam assessment form a cautious mosaic, not a certainty. The approach remains diagnostic, not deterministic, recognizing privacy concerns and false positives. Stakeholders pursue transparency, yet scrutiny ensures utility without compromising autonomy or surrendering control to opaque signals and algorithms.
Practical Steps to Stay Safe: Tools, Limits, and Best Practices
Practical steps to stay safe hinge on concrete tools, explicit limits, and disciplined practices. The detached analysis favors verification hygiene: employ phone verification cautiously, perform spam checks before sharing numbers, and minimize exposure of phone data. Establish boundaries, document safety practices, and audit sources. Skeptical scrutiny reduces risk while preserving access to legitimate networks, preserving freedom without compromising personal control.
Conclusion
A detached observer notes that the hub aggregates signals rather than promises perfect truth. Like a lighthouse that casts warnings without forcing passage, it offers reputation scores and corroborating data to guide decisions. Yet the reader remains wary: numbers can mislead, signals may clash, and privacy matters. The conclusion, therefore, is cautious confidence—trust the system as one more instrument, not a verdict. In the end, vigilant verification prevails, echoing the old caution to tread thoughtfully and verify.