Phone Verification Portal Check by Phone Number Exploring Safe Contact Signals
A phone verification portal should be evaluated for trustworthy contact signals rather than mere functionality. Clear privacy notices, auditable logs, and independent attestations matter. Cross-checked contact details, explicit user consent, and documented response timelines signal legitimacy. Least-privilege access and continuous monitoring reduce risk. The framework invites scrutiny of how ownership is verified and how responses are tracked. Skipping these cues invites uncertainty, leaving questions about safety that demand careful attention.
What Is a Phone Verification Portal and Why It Matters
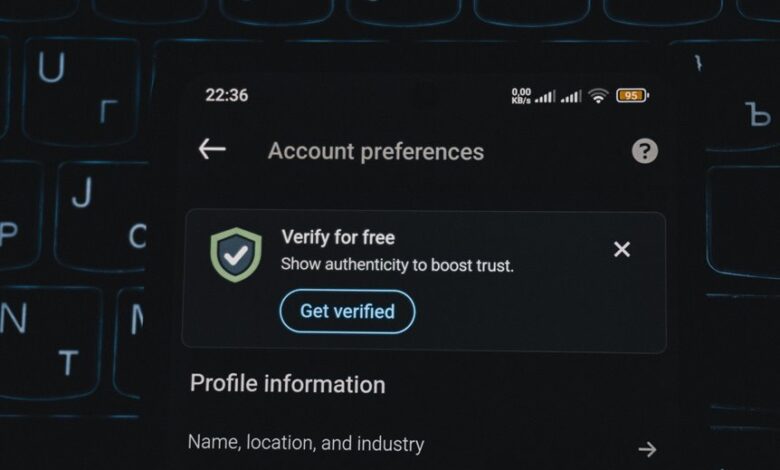
A phone verification portal is a controlled interface that confirms ownership of a telephone number by delivering or requesting a verification signal, then validating the response.
It enables secure access while reducing impersonation risk.
The topic emphasizes security practices and user education, outlining transparent processes, auditability, and user-focused safeguards.
Vigilance ensures freedom through accountable verification, avoiding ambiguous methods and promoting informed, responsible participation.
Signals of a Trustworthy Verification Portal (Safe Contact Signals)
Trustworthy verification portals exhibit distinctive, verifiable indicators that users can rely on without ambiguity. They emit trust signals through clear privacy notices, transparent data handling, and proven identity verification methods. Auditable logs, independent third-party attestations, and consistent security practices reinforce confidence. Users assess legitimacy via cross-checkable contact details and documented response timelines, ensuring timely, accountable verification without compromising autonomy.
How to Use a Verification by Phone Number Workflow Securely
Establishing a secure phone-number verification workflow requires disciplined steps and verifiable controls, ensuring that each interaction minimizes exposure to misuse. The approach emphasizes safe contact signals and auditable traces, enabling independent verification. Adherence to verification workflow best practices reduces risk, supports user autonomy, and maintains privacy. Operators implement least-privilege access, explicit consent, and continuous monitoring to uphold secure, compliant processes.
Red Flags and Scams to Avoid in Verification Portals
Verification portals built for phone-number verification must be scrutinized for common red flags and scam indicators. The analysis highlights red flags such as unexpected requests, opaque processes, and pressure tactics. Awareness of scam tactics, suspicious links, and unverified auditors aids caution. Emphasize safe signals and verifiable trust indicators, including transparent controls and independent verification, to preserve user autonomy and security.
Conclusion
A phone verification portal should foreground user consent, auditable timelines, and least-privilege access to protect ownership and privacy. Transparent privacy notices and independent attestations bolster trust, while cross-checked contact data and timely responses deter impersonation. Vigilant monitoring and continuous improvement are essential to sustain accountability. Example: a hypothetical fintech deployment logs every verification event, flags unusual delays, and provides users with verifiable receipts; when compromised, rapid audit trails enable swift remediation and user notification.