Scam Detection Analysis Node Check Phone Numbers for Scams Revealing Accurate Data

Scam detection nodes assess phone numbers by aggregating signals from calls, reputational scores, consent provenance, and metadata. The approach prioritizes cross-signal validation over single sources and emphasizes timing, frequency, and caller behavior. Results hinge on robust defenses against bias, drift, and overfitting while preserving privacy. Yet limitations persist: false positives, evolving tactics, and data gaps can obscure accuracy. The balance between transparency and action leaves a critical question unresolved as practitioners proceed.
How Scam Detection Analysis Nodes Identify Dubious Numbers
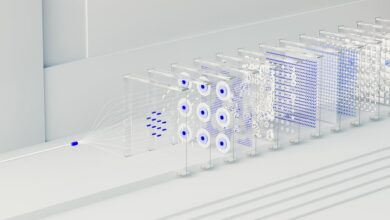
One of the core tasks in Scam Detection Analysis Nodes is to assess the legitimacy of phone numbers by aggregating and scrutinizing multiple data signals. The method catalogues call patterns, reputation scores, and consent provenance to flag dubious numbers, while preserving transparency. Results acknowledge false positives and emphasize user consent, ensuring decisions remain rigorous, verifiable, and aligned with freedom-enhancing analytics.
How Global Blacklists and Call Metadata Combine
Global blacklists and call metadata are integrated to strengthen signal reliability in scam detection analyses. The approach remains data-driven and skeptical, compiling cross-field evidence rather than accepting single-source signals.
Despite apparent cohesion, an unrelated concept can drift into models, creating mislabeling risk. Analysts emphasize validation, transparency, and adversarial testing to prevent overfitting and preserve operational freedom.
Interpreting Signals: Timing, Frequency, and Caller Behavior
Timing, frequency, and caller behavior constitute core signals in scam detection, with each attribute offering distinct causal and correlative value that researchers must verify through controlled evidence; irregularities in patterning require scrutiny to distinguish legitimate variance from adversarial manipulation.
The analysis emphasizes timing patterns and structured caller behavior as measurable, reproducible features, resisting overinterpretation while seeking robust, defendable conclusions about systemic anomalies.
Real‑World Results: Accuracy, Limitations, and Privacy Considerations
Real-world results for scam-detection systems hinge on measured accuracy, clearly defined limitations, and robust privacy safeguards. Verification reveals modest false-positive rates amid diverse caller behavior and evolving heuristics, while scalability challenges constrain deployment in heterogeneous networks. Data privacy remains pivotal: anonymization, access controls, and audit trails reduce risk, yet transfer and retention practices invite scrutiny from freedom-minded stakeholders.
Conclusion
The Scam Detection Analysis Node integrates cross-signal validation to label numbers, reducing reliance on a single source. By weighing timing, call frequency, and behavior alongside consent provenance, it emphasizes verifiable patterns over isolated reports. A hypothetical case—an uptick in rapid, inbound attempts from a previously quiet line coupled with shifting caller IDs—illustrates how multi-signal corroboration can flag risks before user exposure. Yet acknowledged false positives and drift demand continual recalibration and transparent reporting of uncertainties.