Scam Research Portal Check Number for Spam Unlocking Safe Communication

The Scam Research Portal leverages a stable check number to unify disparate spam reports, enabling transparent aggregation and auditable workflows. This approach separates validation from user actions, guiding policy through data-driven thresholds. It supports continuous monitoring and anomaly tracking while promoting safe, evidence-based communication. By balancing security with autonomy, it invites ongoing evaluation of risk signals and stakeholder inputs, leaving a precise question in the air about how such a system scales under evolving threats.
What the Scam Research Portal Is and Why It Helps
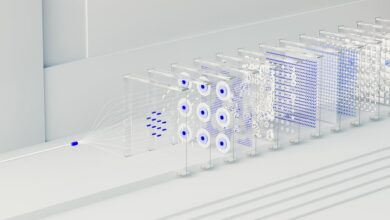
The Scam Research Portal is a centralized resource designed to aggregate and index information about reported scams, enabling users to search, compare, and verify incidents efficiently. It presents structured data and clear provenance, supporting critical assessment without bias. By integrating check number and spam analytics, the portal enhances transparency, enabling informed decisions while preserving user autonomy and freedom to scrutinize sources.
How a Check Number Improves Spam Detection and Response
One clear way a check number enhances spam detection and response is by providing a stable reference that ties disparate reports together, enabling automated systems to aggregate, trace, and compare incident details without relying on subjective recollections.
The mechanism supports verify_keywords and structured risk_assessment, reducing ambiguity while preserving user autonomy, guiding proactive containment, and informing transparent policy decisions.
Step-by-Step: Verifying Messages Without Risk
A practical approach to verifying messages without risk begins by establishing a repeatable, auditable workflow that separates validation from user-facing actions. The analysis targets unverified sources and documents the risk assessment, detailing controls and decision criteria. The process emphasizes cautious scrutiny, immutable logs, and transparency, ensuring stakeholders understand validations while preserving freedom to challenge conclusions without compromising security.
Best Practices for Safe Communication and Ongoing Monitoring
Best Practices for Safe Communication and Ongoing Monitoring requires a structured, evidence-based approach to safeguarding exchanges and sustaining vigilance over evolving threats.
The assessment favors transparent protocols, documented check number workflows, and continuous risk review.
Effective spam detection relies on data-driven thresholds, anomaly tracking, and timely updates.
Decisions remain objective, balancing security with user autonomy, while monitoring ensures adaptive resilience against emerging manipulation tactics.
Conclusion
In a quiet harbor where ships share a single beacon, the Scam Research Portal acts as the steadfast lighthouse. The check number serves as the tide’s rhythm, aligning disparate reports into a single, auditable current. Analysts chart anomalies with cautious, numerical precision, separating validation from action. As ships voyage, ongoing monitoring curbs fog and mirages, guiding policy with data-driven thresholds. The harbor remains open, safe, and transparent, even as unseen storms approach.